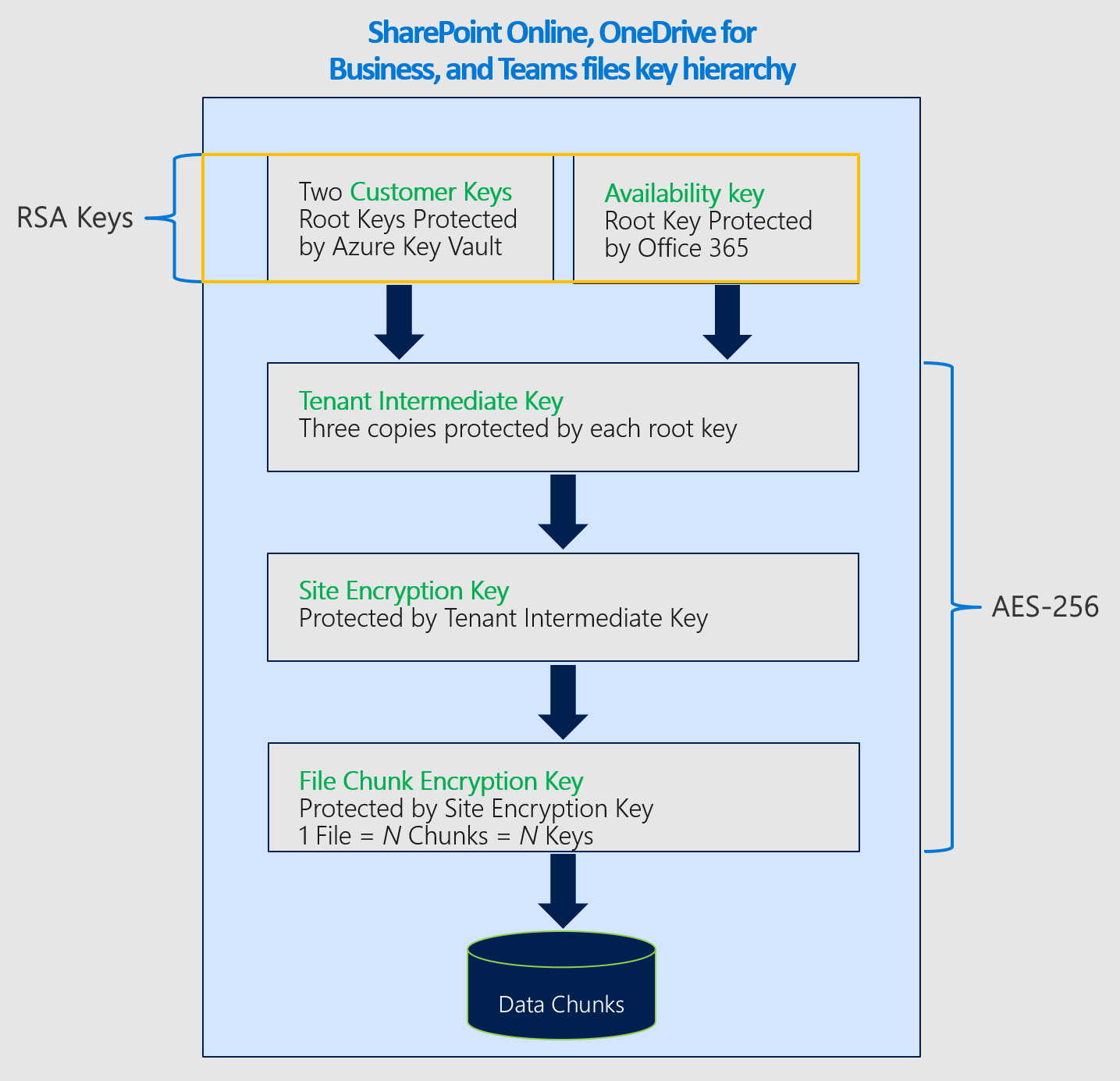
Service encryption with Microsoft Purview Customer Key - Microsoft Purview (compliance) | Microsoft Learn

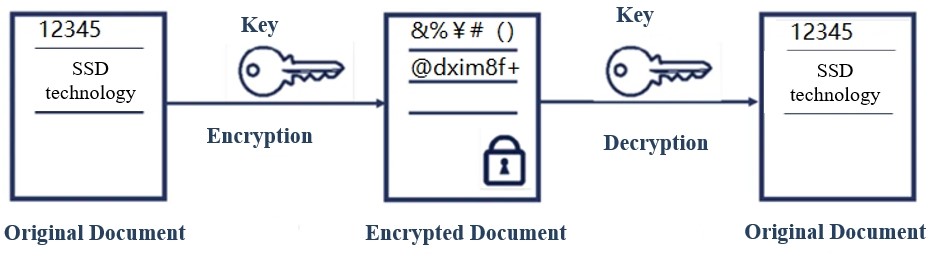
The frame work of the portable hard disk encryption/decryption system... | Download Scientific Diagram
We've introduced 2 new features since our blog on rotating #passwordstate Encryption Keys . You can now set reminders to rotate them and change the encryption between AES 256 Bit and FIPS








![solved] Can't access data after enabling encryption - Pydio Cells - Pydio Forums solved] Can't access data after enabling encryption - Pydio Cells - Pydio Forums](https://global.discourse-cdn.com/standard11/uploads/pydio/original/2X/a/a1a431224ccc1e710ffa40927ae36ac747dc4bad.png)